
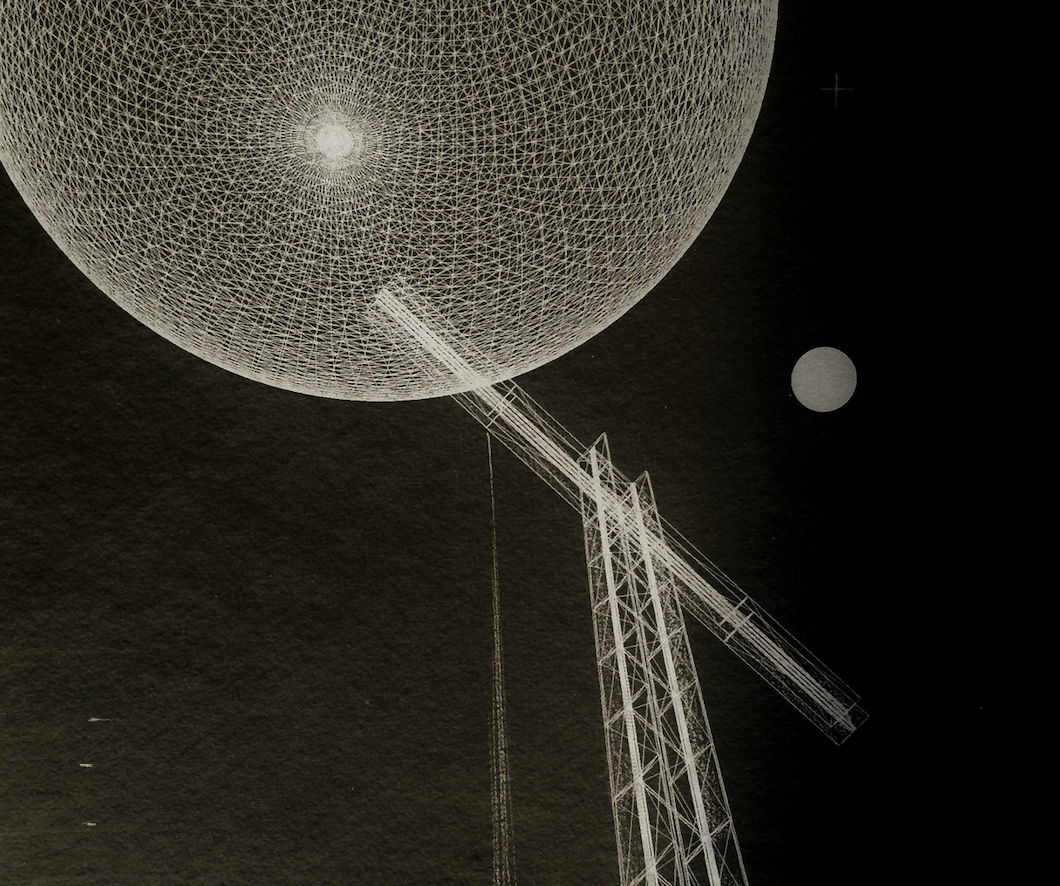
(Sara Gothard, Library of Babel, 2017, in the Jamaica Plain branch of the Boston Public Library, part of their recently digitized art collection.)
We have become familiar with how technology, media, commerce, and forms of human expression are deeply intertwined. Streaming music services and apps like TikTok, and the models behind them, encourage the production of shorter songs that begin with the catchiest riff in the track, so as to maximize quick streams and thus revenue; similarly, when radio airplay was the primary way to push the sales of singles, it helped if the lyrics of a potential hit began with the title of the song, sung before the dial could be turned (just ask the incomparable Nile Rodgers). Despite the protestations of the New York Times art critic, NFTs clearly encourage a specific kind of art, namely one with slight variations on a theme rather than artistic diversity — even on serious subject matters — since the centrality of crypto exchange prods artists to think about the community of owners rather than other audiences for their art, like art critics or the general public.
There is no model consciously shaping the form of this newsletter, or some of the other free newsletters that I read. Obviously that’s not the case for Substackers and big media newsletters. Yet there does seem to be a fairly common format in the genre of the newsletter — one of assemblage and pastiche with commentary, shown here.
For that reason I found Whitney Trettien’s wonderful new book Cut/Copy/Paste to be perfect reading for those of us trying to understand and design the new forms of writing, like newsletters, that have surfaced in digital media. Trettien’s book is a diverse collection of assemblages, including religious books that have been spliced together, reimagined works of poetry, and scrapbooks.

Largely from the seventeenth century, these works show the remarkable fluidity of the codex (and the concept of a library) in ways that parallel our current attempts to make use of pixels on screens to transmit knowledge and opinion. The ways that fragments of older works can be spliced and diced together, and how bookmakers could experiment with forms for different audiences, shows how fertile creativity and craft can accompany and improve new media. It should come as no surprise that there are resonant echos in more modern formats like zines and the digital newsletter.
Cut/Copy/Paste is available in an open access web version, with some nice affordances such as full-color, large images and links to digital libraries and archives, but the print version comes in such a delightful size that it’s worth adding to your personal assembly of books.
Two hundred years ago, long before cryptocurrencies, the blockchain, and NFTs, William Blake maintained a (non-distributed) ledger of people who had bought his illustrated Book of Job:

(William Blake, “Subscribers to & Purchasers of the Book of Illustrations of the History of Job,” Beinecke Library, Yale University, 1823-1826.)
Blake’s ledger recorded more success than The Whitworth Gallery’s digital ledger of its minted William Blake NFTs, which in the last year has seen only 10 sales out 52 available nifties. You can get yours for only ~£2000 (varies wildly with the wildly varying price of Tezos cryptocurrency), with proceeds going toward funding social projects in Manchester.
I’ve been intrigued recently by remotely controlled scientific instruments and the emerging idea of the automated lab. It’s not just the whiz-bang nature of such a thing, which seems inevitable given the direction of technology, but the changes it presents to the nature of scientific research. Gaze upon Carnegie Mellon University’s Cloud Lab Project:

During grad school I lived with chemistry doctoral students, who would often carry around multiple timers that would alert them to when they needed to go back to the lab to stir something or add a solution or test a result. (Sometimes it was during the middle of the night.) New machines take care of all of that, including measurements, titrations, the timing of heating and cooling, and many forms of analysis. And more intriguingly, these robotic devices can be placed anywhere and accessed online; all you need to do to run an experiment is write a bit of code. So much for those timers and the campus chem lab.
Once you divorce place, instrumentation, technical lab knowledge, and researchers, the decentralized, automated model reveals some great improvements. In the same way that the digitization of books and resources such as HathiTrust have allowed researchers who are at institutions with smaller libraries, or independent scholars without a research library at all, to do the kind of work that formerly only the privileged could do, the Cloud Lab potentially broadens access to research that usually required a nearby, often very expensive facility. (There are, of course, still huge costs here, and access is limited to those who can pay the costs, thus my emphasis on broadened rather than open access. But still, you can see the latent potential for even wider access in the future.)
Second, because experiments have now been reduced to bits of code — recipes —they can be more easily replicated by others. So we have a fascinating combination of both the beginnings of the democratization of the lab (you don’t need to be at a university with a fancy, pricey lab to do the work), and the ability to re-run experiments at will (you can replicate an experiment with the right recipe and a click).
This combination of enlarged access and increased accountability seems rare in today’s technological environment, and worth highlighting. Too often adding access entails the creeping lack of accountability, putting democratization in tension with responsibility. (Just witness what has happened on the web and in social media.) So I am eagerly following where this lab experiment heads once it scales (I hope) beyond wealthy universities.
Here’s much more from CMU’s team on the concept and function of the Cloud Lab.
Ah, the 1980s, when computer magazines had joyous, goofy illustrations in them.

(Peter Bentley, illustration for “The Art of the FOR…NEXT Loop, Input Magazine, 1984, Vol. 1, No. 1, p. 16.)
Subscribe to the Humane Ingenuity newsletter:




















 (Alice Baber,
(Alice Baber, 




 (Roger Brown,
(Roger Brown, 


 (Recliners + the scrolling text of a book on the ceiling, yes please.)
(Recliners + the scrolling text of a book on the ceiling, yes please.)










 (Jason Mittell,
(Jason Mittell,  (Jason Mittell,
(Jason Mittell, 


 (Jason Mittell,
(Jason Mittell, 



 (Jeannie Meejin Yoon,
(Jeannie Meejin Yoon, 
 (Julie Chen,
(Julie Chen,  (David Stairs,
(David Stairs, 


